This article will illustrate how to pull the public TLS certificate to Prevent Email using openssl on Linux. There is an openssl package for Windows but it requires installing software. If that's not available, any Linux system can do this.
If you are using TLS for prevent email and need to get the next hop's TLS public certificate, this is much faster than trying to get it from the hosting provider. If you're ''not'' on the Prevent Email server, any Linux system will work for this, you'll just need a way to copy the public certificate or text from the console window.
1. In Prevent Email as the protect user:
openssl s_client -connect <SERVER_HOST_OR_IP>:25 -starttls smtp | openssl x509 -text
This opens a connection so once you get the data, hit CTRL-C to kill the connection.
This example is truncated output, you'll see more information about the certificate above this block you can use to verify you're on the right server. <br />
Change <SERVER_HOST_OR_IP> to the IP or FQDN of the server you're trying to send mail to. If the system is not accepting mail on port 25, change it to the correct port. The rest of the command will not need to be modified for port changes.
2. You'll want to copy the data starting with -----BEGIN CERTIFICATE and ending with END CERTIFICATE-----
Make sure there are not spaces before or after the required data in the file you're saving!
Example:
-----BEGIN CERTIFICATE-----
MIIDEDCCAfigAwIBAgIQQyOcKZQPhbhDU2o35dSoCzANBgkqhkiG9w0BAQUFADAU
MRIwEAYDVQQDEwlkb21haW5zdnIwHhcNMTMwMjA2MTM0NDIxWhcNMTgwMjA2MTM0
NDIxWjAUMRIwEAYDVQQDEwlkb21haW5zdnIwggEiMA0GCSqGSIb3DQEBAQUAA4IB
DwAwggEKAoIBAQCrtST2EFpUQM1cT23H+h+2OZMDS6Ch28kinbnod1ztH62/n+Fv
21O1h5yd7MULfIXmlZJjhoLZlRbWdCgAEBfbwhv889Nw6NBTF1wi5EV2uywdjdX+
I4N34yhdlwLYxqnyx1hZ6WzDcAaUrejGiBLRWmSqrbsWK4syEg8B28Ogw/ukZggD
0JaRopm39Mob4W7DpfAkMiYq/1SmmIsK7khnUhMGPLxPVbvjBNlqMFftD5RtCse8
H8pqr86uygZjMWn8ax63WlPjJkktibUWjaUm9KcI2FUGf6OqFtbfLRR62Dq91O3t
N+IRPSHL7tIgkWNUfwokxp1rPvB6wMTCkAyRAgMBAAGjXjBcMA4GA1UdDwEB/wQE
AwIFoDAnBgNVHREEIDAegglkb21haW5zdnKCEWRvbWFpbnN2ci5sYWIuY29tMBMG
A1UdJQQMMAoGCCsGAQUFBwMBMAwGA1UdEwEB/wQCMAAwDQYJKoZIhvcNAQEFBQAD
ggEBABpRlFdRKnQnNOl3AkY+/Ocw14XlzQUcyeCldSRr4ZDZziO5L/X1lSszZvDr
Y2cvAJEVqGJBVUDpGM9NuDjKwmHE26B0yozNQNNcbvVSscRYnKCo19wSI/xZC0zv
dWfy1wH12/gqvQx7HVaDLAH4KoquUS44gczl12TmMoTZGb1168QQmydun5ylXbAo
GDCM1ky9gJW0RkDICgn8UAX6a6NGSZY09nMB9gyGyZ3eNuHKtHmYJwjoKtk+WvRJ
EM8y78vClBXqrbIzL+slcZWtWG5A/EEa7/uTfpRqt4aILLw8Kn9nGXiFNApt3ydd
ksVCv7H928rRG3MmEZ7TO+dJWBI=
-----END CERTIFICATE-----
3. Now save this in a file on the Prevent Email system. You can copy/paste using VI or Emacs. Save as something meaningful with the .pem extension.
If you need to move this file to the Prevent Email system, do so now.
4. As the protect user, import the file into the DLP keystore:
cd /opt/Symantec/Protect/jre/bin
./keytool -importcert -alias <NAME> -file /home/protect/<FILE_NAME>.pem -keystore ../../Protect/keystore/prevent.ks
**To create a new keystore "prevent.ks" file, simply run the import command above and instead of prevent.ks use a new name like preventNew.ks. Then backup the old prevent.ks file and rename the new preventNew.ks to prevent.ks
./keytool -importcert -alias <NAME> -file /home/protect/<FILE_NAME>.pem -keystore ../../Protect/keystore/preventNew.ks
Where -alias <NAME> is whatever you want to call it (something meaningful is a good idea) in Prevent Email and <FILE_NAME>.pem is the path with file name where you saved it. In this example I saved it in the protect users home directory.
You'll be asked for the keystore password (dummypass by default). It will also display information about the certificate before import and ask if you want to import. Type yes. At this point you should be good to go.
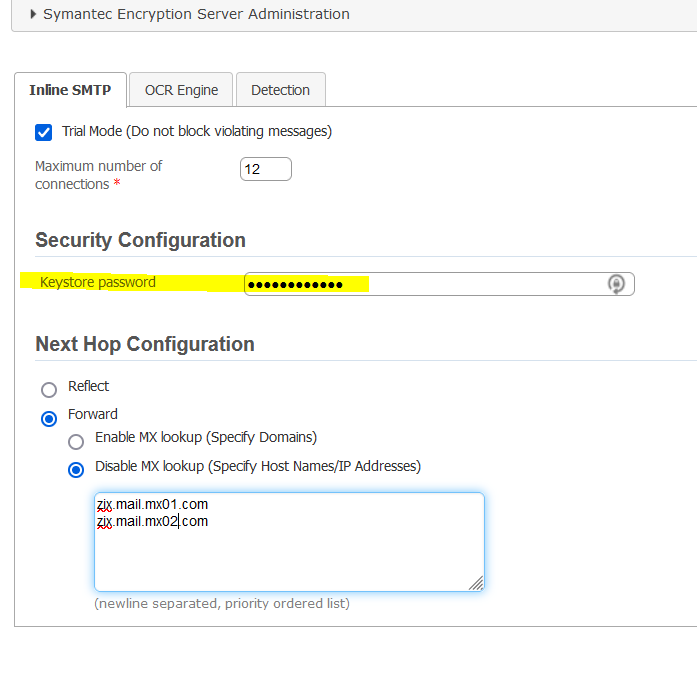
5. Update the keystore password on Enforce Management Web Console > NPE > Configure
6. Recycle the Detection server via the Enforce Management Web Console > NPE
=====================================================================
TIP: Issue below commands if telnet connection is established:
3. Issue below commands if telnet connection is established:
EHLO <your mail server domain>
MAIL FROM:<sender@domain.com>
RCPT TO:<recipient@remotedomain.com>
Type DATA
If desired, type message text, press ENTER, type a period (.), and then press ENTER again.
If mail is working properly, you should see a response similar to the following indicating that mail is queued for delivery.
0 Comments